Thanks for reporting.
I’ve had several beta users have reported issues with PhotoStructure on Windows when using third-party antivirus/antimalware packages.
Due to these false-positives, and the fact that these software packages have a history of security issues themselves, PhotoStructure on Windows is only supported when used with Microsoft Defender Antivirus.
Microsoft Defender Antivirus is the free and built-in antivirus for Windows 10 that was previously called Windows Defender.
I recommend all my Windows users get in the habit of using https://www.virustotal.com to scan any download. VirusTotal isn’t software you install: it’s a website that you drag the downloaded app onto, and it scans the app with some 50-odd virus scanners for free.
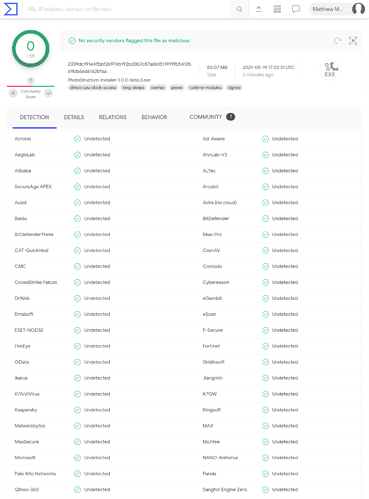
Here are the VirusTotal scans of the .7z installer package for v0.9.1 (one for the file, one for the URI):
And for v1.0.0-alpha.7
Someone else just reported this, and I figured I could give a bit more background on how I ensure PhotoStructure’s builds are as secure/free from malware as I can make them:
-
I always update all of PhotoStructure’s dependencies and then run security audits (using snyk) to those dependencies right before a release. Electronegativity audits run against the desktop build, as well.
-
The final windows distribution builds are done on computers that are, for the most part, off, and run full offline antivirus scans before builds.
-
All binaries are signed with extended-verification code signatures.
-
All code commits are GPG-signed, periodically re-verified, and pushed to multiple remote repos, to detect tampering on either repo.
-
All git and related logins are protected via hardware tokens where possible, or 2FA.
-
The windows installer now contains the full installer (version 0.9.1 and earlier used the “Web installer” feature of NSIS, which meant the installer was very small, and when run, downloaded the installable archive in the background). This means you can run virustotal on the installer and be assured you’re scanning the whole payload.
As always, if you see anything suspicious, better safe than sorry: please tell me and we can look at it together, but always have at least one backup, and preferably have at least one offline or offsite:
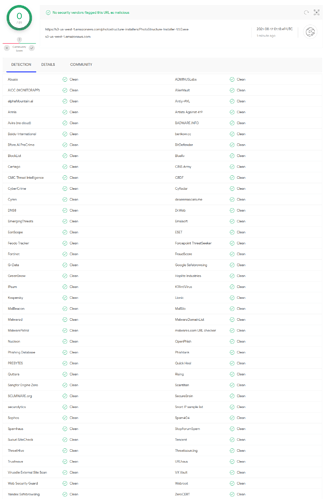
Another update: I just submitted the beta.3 windows build to virustotal, and (thankfully) all green:
Here’s version 1.1.0:
As of today this is reporting a single flag for the 1.1.0 windows installer:
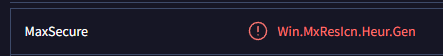
edit: went away after doing a reanalyze ![]()